UPDATE: Launch was a complete success! A full write-up will be coming in due course…
The next Project Horus launch is currently planned to fly on Sunday the 25th of August(weather permitting), with a planned launch time of 10AM. As usual, there’s always the chance the weather for the planned launch date may not be suitable, so if necessary, the backup launch date will be Sunday the 1st of September.
The launch site will be the usual Mt Barker High School Oval. Launch crews should be on-site around 9AM. If you haven’t attended one of our launches before, this is a great opportunity to come along and see what’s involved first-hand!
WiFi Pineapple Payload
This flight will be the first of hopefully many more payloads proposed and developed by AREG club members under the Project Horus Member Payload Launch Program. Derek VK5TCP’s payload is a WiFi Pineapple board – a WiFi penetration testing device developed by Hak5. The payload will be ‘war-ballooning‘ throughout the flight, recording the SSID of all WiFi access points it can receive signals from. It will also be broadcasting an open WiFi access point (‘VK5ARG’) on the 2.4 GHz band. The payload will be using a ~11 dBi patch antenna pointed directly downwards.
To encourage community participation in this launch, there are two challenges associated with this payload:
- Get your Access Point SSID observed by the payload! – Set up a WiFi Access point connected to a high gain antenna pointed at the payload. After the flight we will publish a list of all SSID’s that were observed, and at what altitude they were spotted. For your best chance at being observed, beacon using the lower-speed 802.11b mode.
- Recover the secret message! – Connect to the access point on the balloon while it is in flight and retrieve a secret message from a web server running on the payload. This will be a serious challenge to achieve, and will require the use of high-gain antennas on the ground. Our link budgeting suggests that the full 4W of allowable LIPD Class License EIRP will be required to connect to the payload. Amateur radio operators with an advanced license are permitted to use any power level up to the limits of their license conditions. The web server will be running on the IP address 172.16.42.1, and clients can either accept a DHCP lease, or use a static IP address between 172.16.42.150 and 172.16.42.200.
To have the highest chance of success, stations will need to be situated directly underneath the flight path, with antennas pointing upwards to the payload. A map of the predicted flight path will be posted closer to the launch date.
Wenet Imagery Payloads
This flight will also fly a ‘Wenet’ high-speed imagery payload, as have been flown on many previous Horus launches. The centre frequencies for this transmission will be 441.200 MHz. This payload will be downlinking HD pictures throughout the flight, which will be available at this link:
Reception of the Wenet signal requires a RTLSDR and a Linux PC/Laptop. Instructions on how to set up the required software are available here.
Telemetry Payloads
As always, we’ll be flying the usual assortment of telemetry payloads, including:
- Our usual 100 baud 7N2 RTTY telemetry on 434.650 MHz USB. This can be decoded using dl-fldigi, with a reception guide available here. Recent testing of dl-fldigi’s decode performance has found that the auto-configured RTTY receive bandwidth is too narrow, and can detrimentally impact decode performance (by up to 3dB!).
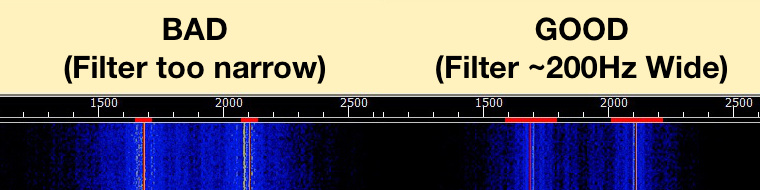 To fix this, open dl-fldigi, and in the Configure menu, select Modems, and then go to the ‘RTTY’ tab. Drag the ‘Receive filter bandwidth’ slider to 200, then click ‘Save’. Note that this setting will be reset whenever you hit the ‘Auto-Configure’ button!
To fix this, open dl-fldigi, and in the Configure menu, select Modems, and then go to the ‘RTTY’ tab. Drag the ‘Receive filter bandwidth’ slider to 200, then click ‘Save’. Note that this setting will be reset whenever you hit the ‘Auto-Configure’ button! -

4FSK Telemetry decoder
The new 4FSK Binary telemetry will be transmitting on 434.660 MHz USB. This uses a separate decoder, with setup instructions for this available here. This telemetry payload will soon become the primary method of tracking the flight – the RTTY payload is expected to be retired in a few launches time.
 Tracking of the flight will be available on the HabHub Tracker, available at this link. (Note that other balloon launches will also be visible on this page, including the Bureau of Meteorology launches from Adelaide Airport).
Tracking of the flight will be available on the HabHub Tracker, available at this link. (Note that other balloon launches will also be visible on this page, including the Bureau of Meteorology launches from Adelaide Airport).



